Much has been written about how COVID-19 has impacted cybersecurity during 2020, from heightened cybersecurity threats to foundationally challenging business resiliency. However, there are other lessons for cybersecurity which are unnoticed or under-emphasized. Swiss...
Abusing Qualcomm EDL Mode for Device Capture

EDL acquisitions are one of many ways you can bypass passcodes and gain physical access to many Android devices with Qualcomm based chipsets. Emergency Download (EDL) mode is a Qualcomm feature that can allow you to recover data from a device and perform tasks like unbricking or flashing the device. On supported devices, we can use EDL to extract a full image.
The method for putting a device into EDL mode can vary depending on the model. There are three ways to put a device into EDL mode and no single method works on all phones. On some devices you can use a special cable, while others might require you to disassemble the device. Finally, if the device is unlocked, you can use ADB or fastboot to reboot the phone into EDL mode. Below you can find instructions for all three methods, so you can get comfortable performing them to make use of this acquisition method.
EDL Cable
Using a special cable to put the phone into EDL mode is probably the easiest method listed here. The cable is designed with a toggle switch to short out the correct data pin and force the phone into EDL mode.
You can buy these cables and they are often included in commercial forensic solutions.
Once you have the cable, the workflow is straight forward. Just plug the cable into the computer, press and hold the toggle button and plug it into the phone. After releasing the toggle button, the phone should boot into EDL mode.
If you’re not sure the phone is in EDL mode, check Windows Device Manager for any Qualcomm devices listed under COM Ports which should confirm the device is in EDL mode and ready to go. Once the phone is in EDL mode, you’re free to continue with the acquisition.
JTAG / Test Pin
If the cable method doesn’t work, another helpful method is to short out the CMD pin on the test ports to direct the device to boot into EDL mode. Not all devices have JTAG test ports, but if they do, this method works quite well. https://alephsecurity.com/2018/01/22/qualcomm-edl-1/ (this link also gives a great write up on the EDL exploit and how it works as well).
Once you’ve opened up the device and found the necessary test ports, you can short them with a pair of tweezers or something else metallic while inserting the USB cable into the device. This method works quite well on many devices that are susceptible to the EDL exploit but as mentioned previously, won’t work on all devices.
ADB
Finally, the last method available is limited to devices that have ADB access enabled. This means the phone must be on, unlocked, and USB debugging turned on so that you’re able to send and receive ADB commands to the phone. This won’t always be the case if you’re dealing with a locked phone but the method does work quite well in scenarios where the phone is already unlocked and you just want to get a better acquisition.
Once you have ADB access, simply send the command “adb reboot edl” over the command line and the phone will reboot into EDL mode. From there continue with your EDL exploit and acquisition like the rest.[1]
Data Extraction
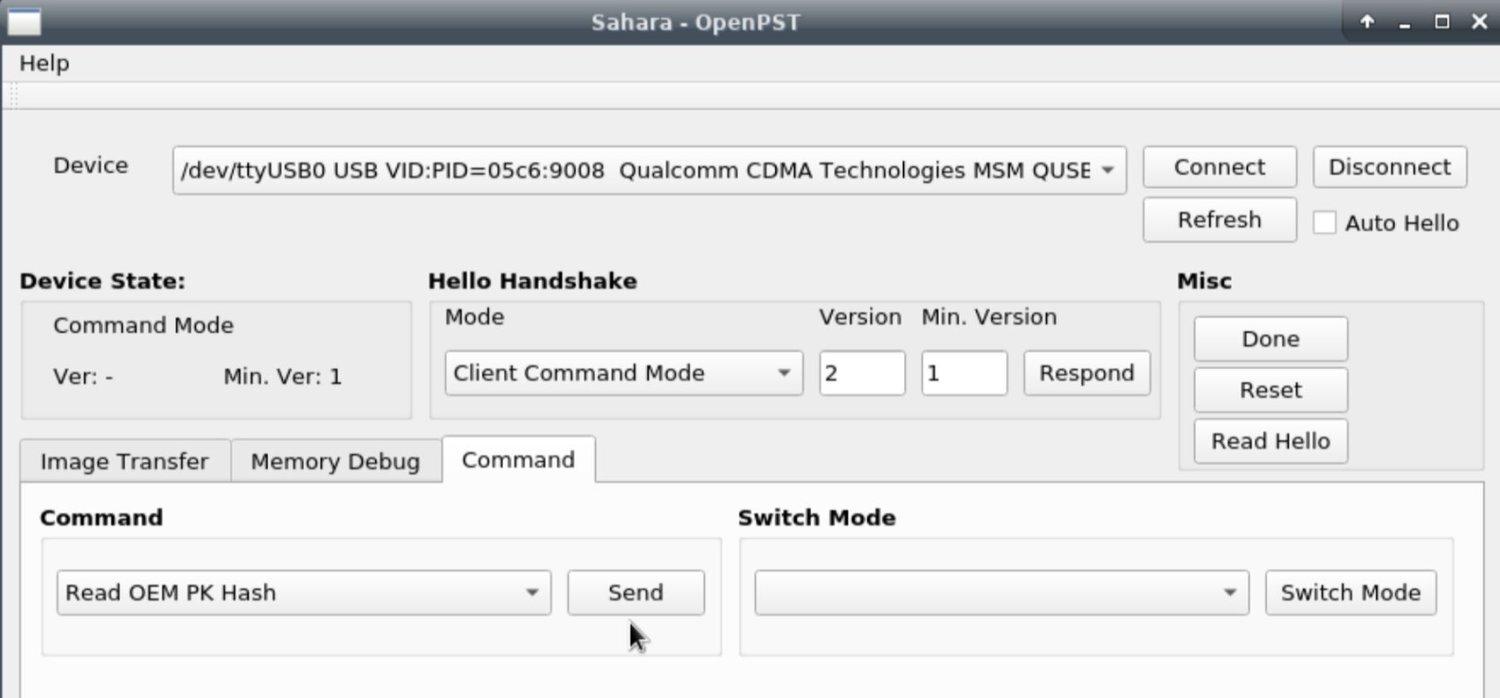
Once a device is in EDL mode (9008 mode) OpenPST Sahara (https://github.com/openpst/sahara) can be used to communicate with the device. A full acquisition will require advanced tooling often found in commercial forensic tools.