Risk Summary
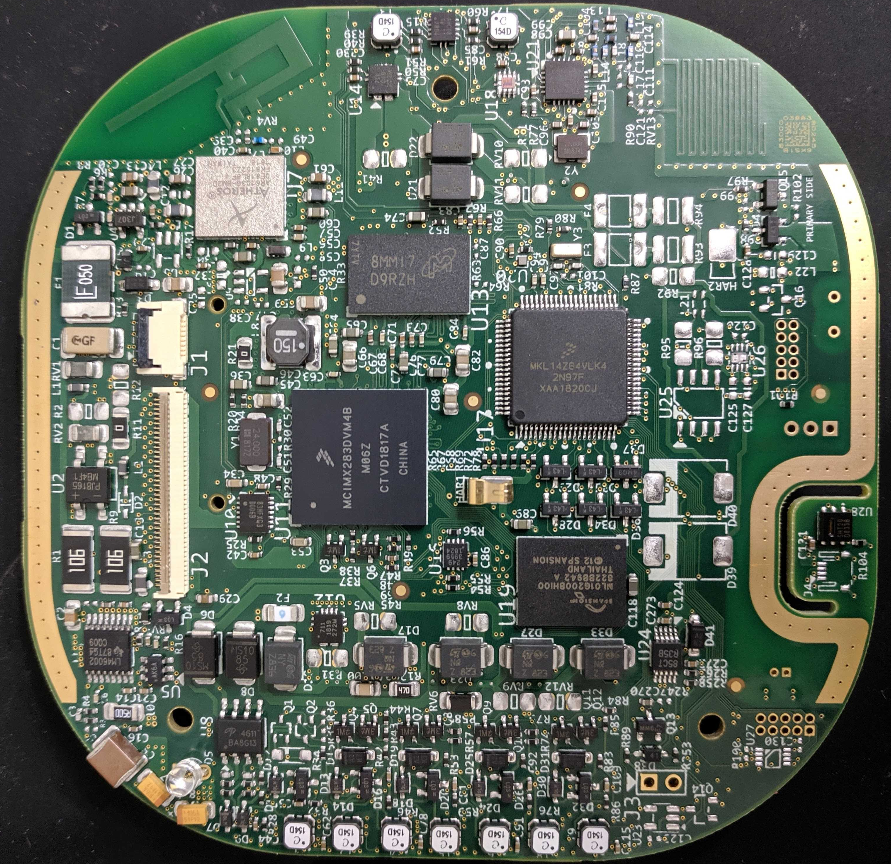
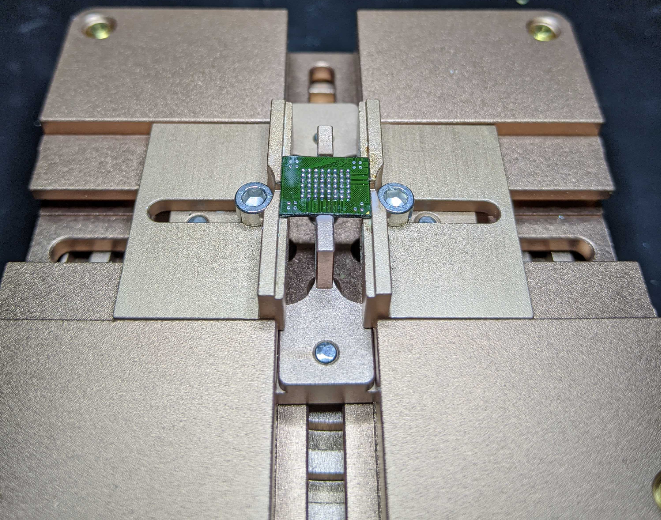
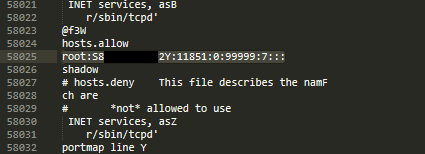
The ecobee3 lite device does not use encryption on the NAND flash storage. The device firmware as well as user information is stored on the flash chip. A threat actor with physical access to the ecobee3 lite device can extract sensitive data from the flash storage by removing the NAND flash chip and connecting directly to the flash chip using the parallel flash reader.
With a copy of the device firmware, a threat actor can perform offline analysis to identify vulnerabilities in the device, including recovering the root password.